Report
Question Description
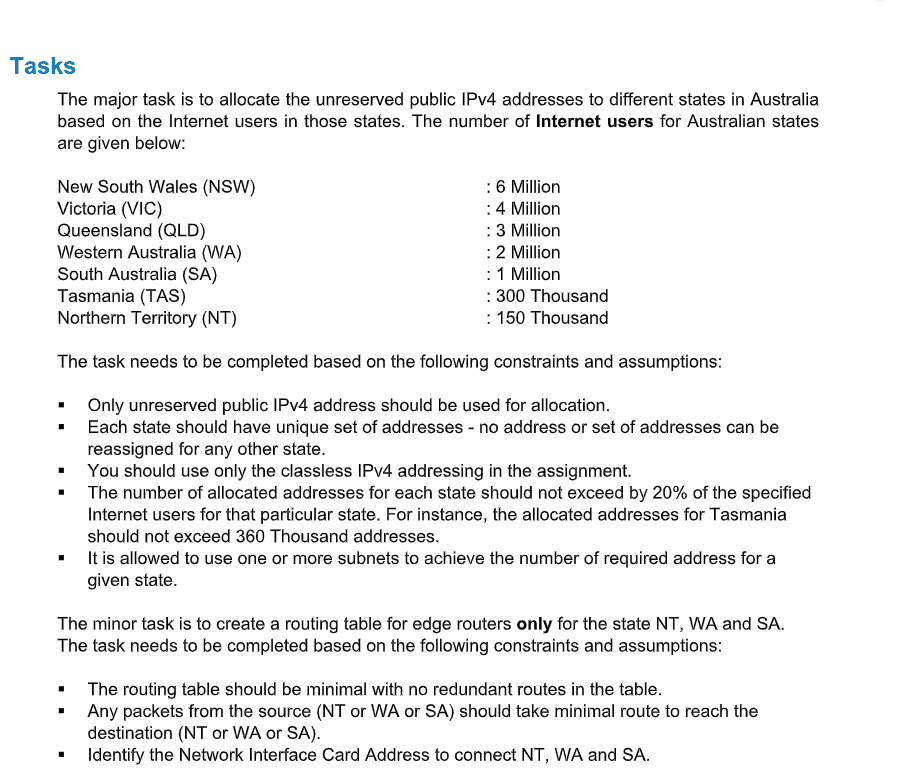
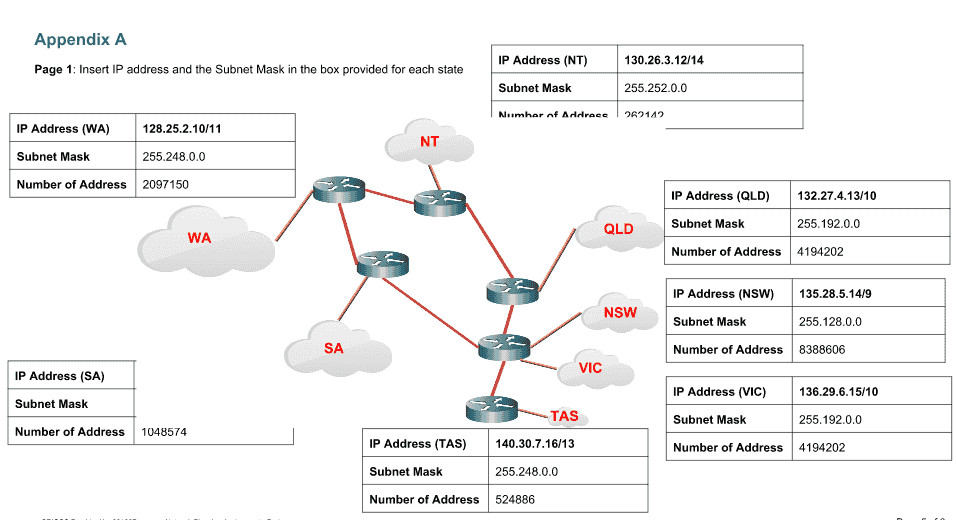
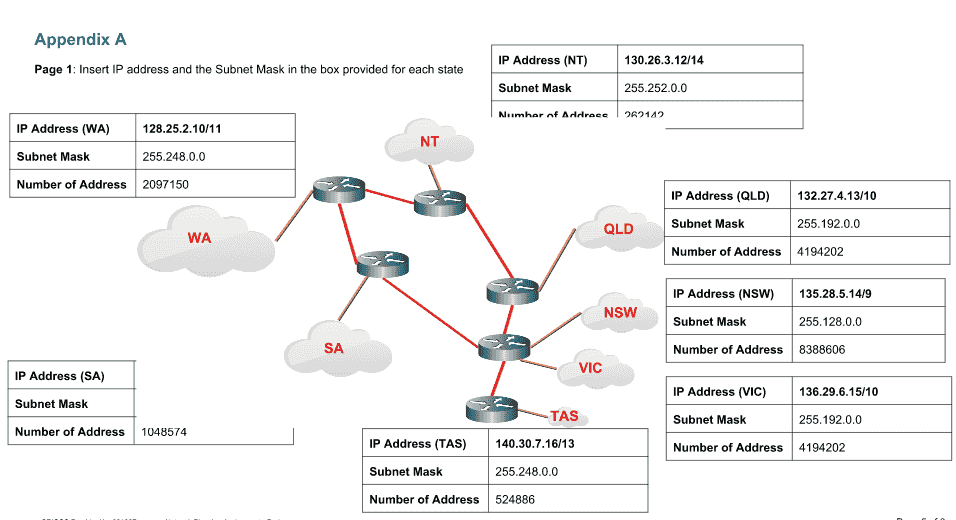
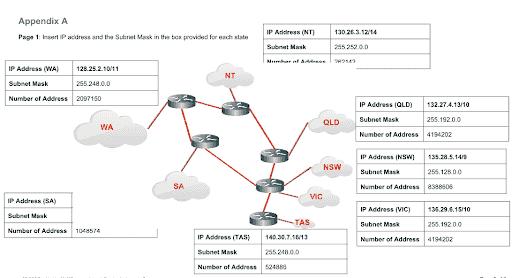
Read the document and you need to amend all the tasks and show in appendices.
Task
- As described in the case study above, the source of the current problem is the Remote Access Server, which has allowed cyber attacks to be launched from the vendor’s network. Given the current business needs of the organisation, eliminating access to the Web Server is not a solution. Explain a potential scenario where a DOS attack could occur from the vendor’s network against the Web Server. Ensure you explicitly state any assumptions made. You are encouraged to use the network diagram provided to add annotations to support your answer.
- Propose a solution to address the cyber attack described above. Ensure you justify your solutions and substantiate with relevant evidence. You are encouraged to use the network diagram provided to add annotations to support your answer.
- List potential evidence that can be acquired using the IDS to support the preliminary endings. Here evidence means, any information that can be gathered using the snort IDS to assist in identifying the source/nature of the cyber attack.
- Explain in detail, how you would congure/tune the IDS to effectively serve its purpose as described in the case study. This would include activities such as but not limited to changes to the conguration le, IDS rules, logs generated, etc.
- Implement the solution you have explained in step 4 in the IDS VM, and demonstrate that it works by performing a DOS attack against the Web Server. You may use a separate Kali VM connected to the same subnet as the Web Server and IDS. You can achieve this by putting all three VMs in the same virtual network (e.g. vmnet4) in Vmware.
Resources
Network Diagram (draw.io format) attached above VMs (shared in Box, please check your student email for invitation. If you haven't received, email ahmed.ibrahim@ecu.edu.au to request access ASAP)
Solution